Overview
Register your Google Compute Engine cloud account with RightScale so that you can use the Dashboard to manage your Google Compute Engine cloud resources.
RightScale uses Google Service Accounts to interact with your Google Cloud Platform project. The Service Account does not need to exist in the project that you are registering, but it must have access to the project as defined below.
Prerequisites
- You have the project ID of the project you wish to register
- The project has Google Cloud APIs enabled (this is the default setting for cloud projects)
- A Google Service Account has been created
- You have the JSON private key for the service account
- You have enough privileges on the project to grant the service account an IAM role (for example, 'Project Owner')
- You have
adminorenterprise_manageron the RightScale account you wish to register the project with - The RightScale account does not currently have a Google project registered with it
Connecting RightScale to GCE
Grant the service account IAM access to the project
In order for the service account to be able to manipulate resources in the project, it must be granted an IAM role on the project. When granting roles, you can use either the Viewer role to grant RightScale read-only access, or the Editor role to take full advantage of the features in RightScale.
Follow the steps below to add the IAM role to the service account if this is not already configured.
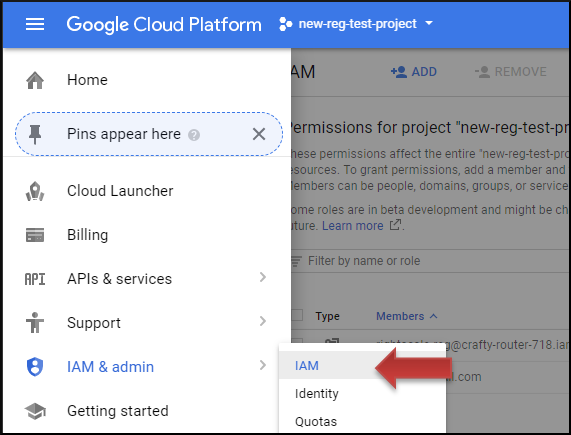
In Google cloud console, navigate to the project you wish to register
From the left menu, select
IAM & admin
->IAM
Click the
Add
button on top of the IAM page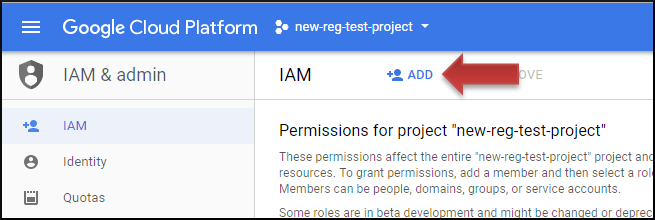
Enter the ID of the service account and use the Roles dropdown to select Project -> Editor (or Project -> Viewer for read-only access) and click
Add
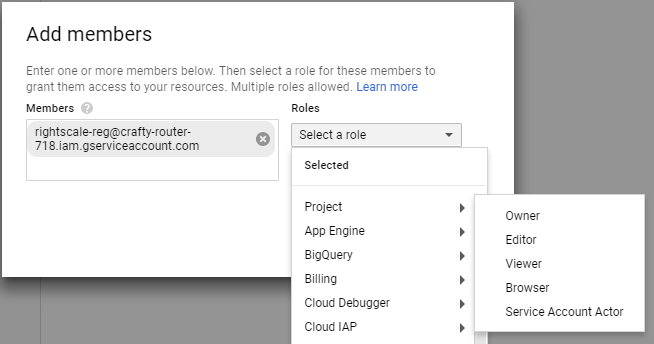
Now that the service account has access to the project, you can use the service account credentials to register the project with RightScale in the step below.
Register the Project with RightScale
The following instructions are for registering using the Cloud Management UI. If you would prefer using an API call to register the project, see the API documentation examples
In order for RightScale to interact with the Project, you must provide the service account credentials and specify which project to link to the RightScale account.
In RightScale, select the account you wish to register the project with
Using the top menu, select
Clouds
->Add Cloud
(note: if you do not seeAdd cloud
, you do not have enough permissions to add a cloud) and then press theConnect to a Cloud
button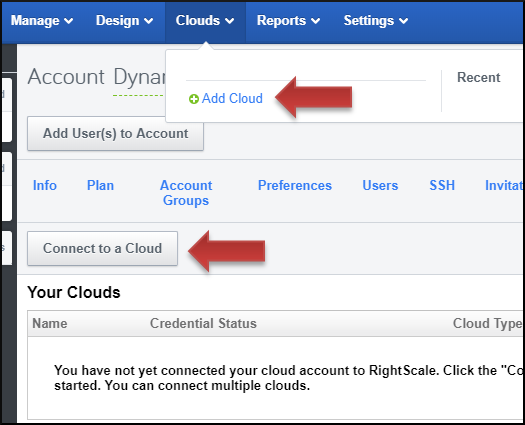
Select
Google
from the list on the left (note: if you do not seeGoogle
, this is because you have already registered a Google project with this RightScale account -- select a different account or create a new RightScale account to register this project)In the dialog that opens, enter the Project ID of the project you want to connect and upload the JSON key file for the service account
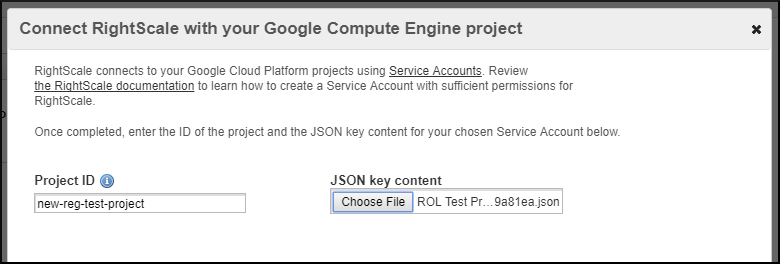
Click Continue
The system will perform a quick check to ensure that the key file is correct and provides the required access to the Google Project
Next Steps
Once you have registered your project, you will see that the Google cloud is enabled
under the Clouds tab in the Dashboard. It may take several minutes, but all of your Google Compute Engine resources are now visible under the Clouds menu (Clouds > Google).
Update your account to use Service Account
First, ensure you have met all of the prerequisites listed earlier on this page.
It is considered best practices to rotate your keys periodically. To rotate service account credentials, first create a new key for the service account.
The following instructions are for updating credentials using the Cloud Management UI. If you would prefer using an API call to update credentials, see the API documentation examples.
Follow these steps in all RightScale accounts registered with projects using that service account:
In RightScale Cloud Management, navigate using the top menu to Settings -> Account Settings -> Clouds
Click on the pencil icon next to
Google
cloud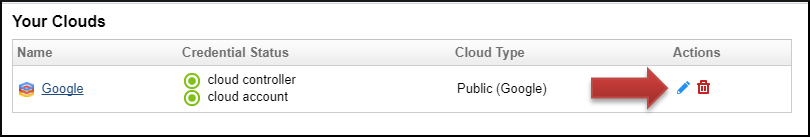
Select the
Update service account credentials
option, select your new key file, and pressUpdate
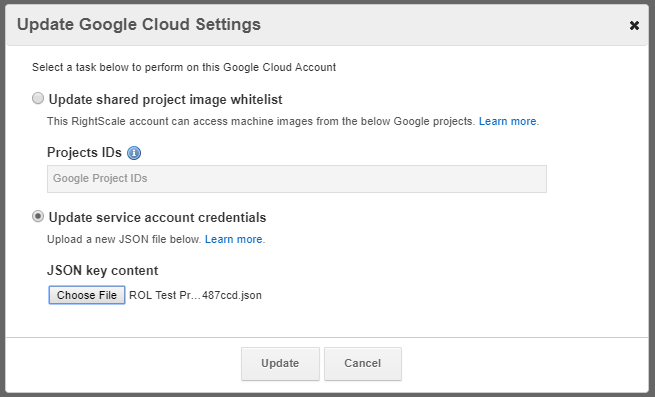
Once all accounts have been updated with the new keys, you can delete the old key from Google.
Why is RightScale requesting customers to use Google Service Accounts?
Google Service Accounts are new and were not available when RightScale implementd GCE support.
TroubleShooting
Error During Registration
If you are seeing a red error during registration that says something to the effect of: Project 'your-project' is not accessible, check the following:
- you have enabled the Google Cloud APIs
- the service account has IAM permissions on the project you are registering
- the key file you are using is still valid